sec boot 使用文档¶
密钥生成¶
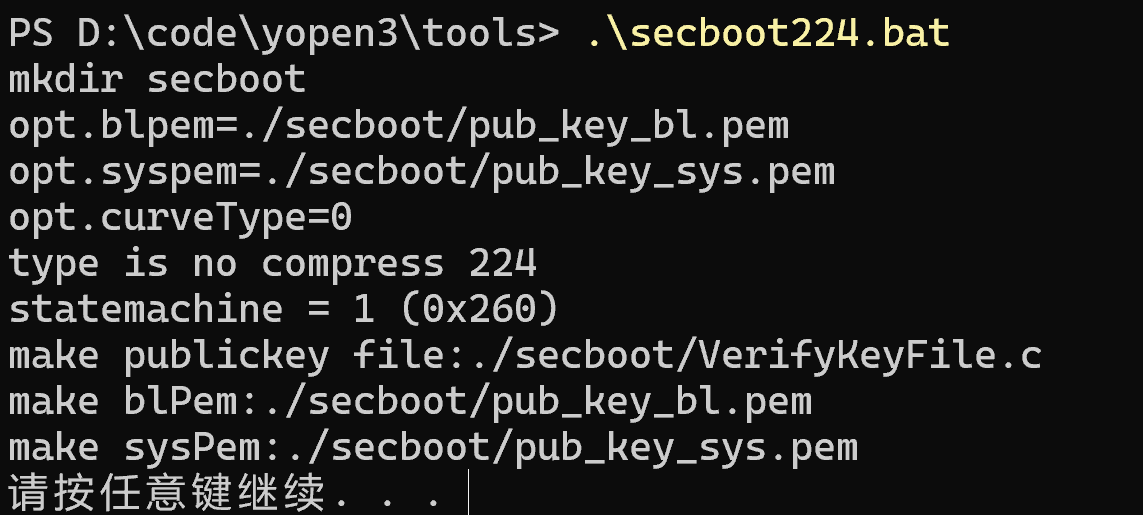
- 运行tools\secboot224.bat, 如下图所示
- 生成的内容
注:生成的三个文件一定要做好备份,防止板子签名后无法下载软件¶
注:生成的三个文件一定要做好备份,防止板子签名后无法下载软件¶
注:生成的三个文件一定要做好备份,防止板子签名后无法下载软件¶
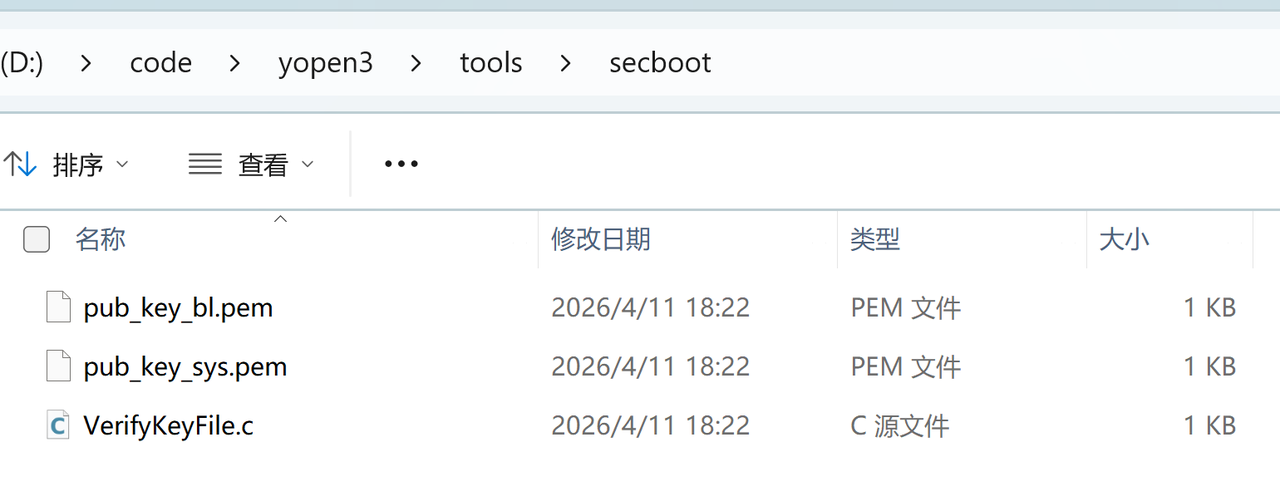
-
pub_key_bl.pem和pub_key_sys.pem : 在编译项目的时候,会使用tools\secboot目录下的pub_key_bl.pem和pub_key_sys.pem对 BL,SYS bin 做签名,分别生成两个签名头bin文件(bl_sec_header.bin和sys_sec_header.bin), 然后打包进binpkg中
-
VerifyKeyFile.c 文件内容如下, 会在g_partiontable变量中直接引用下面数组
const unsigned char blPubKey[56] = {0xa8,0xfa,0xe6,0xfe,0x68,0x78,0x3c,0x70,0x4,0x7a,0x97,0xc8,0xbb,0x6a,0x22,0xeb,0xc1,0xa7,0x61,0x99,0xd6,0x4d,0xf3,0x6e,0xb1,0xdf,0xdf,0x6,0xe3,0x3d,0xdc,0x40,0x83,0x4a,0x7c,0x6b,0x4e,0xdd,0xdd,0x64,0xf0,0x42,0x71,0xba,0x7f,0xe2,0x3a,0x67,0x62,0x19,0xab,0xb6,0x1d,0x30,0x33,0xc8};
const unsigned char gVerifyPubKey[56] = {0x7d,0x46,0x37,0x35,0xe5,0x98,0x93,0x65,0xac,0xa0,0xa1,0xaf,0x6b,0x2e,0x55,0xfc,0xa8,0xf8,0x67,0xf0,0x29,0x46,0x95,0xab,0x31,0xee,0x5,0x3f,0x8,0x1,0xef,0x16,0xe5,0x17,0xda,0x77,0x84,0x4c,0x5c,0xb7,0xc0,0xcb,0xb,0xff,0x22,0x69,0x56,0x44,0x55,0x25,0x2d,0x3c,0x7f,0xb6,0xd1,0x40};
代码修改¶
- 修改bsp\EC7XX\kernel\PLAT\project\ec7xx_0h00\ap\apps\yopen_app\src\bsp_custom.c文件, 在g_partiontable变量中添加.secBootTable 成员的初始化, 内容就是VerifyKeyFile.c 中的2个数组, 并将magicnumber 改成 0x12345678. (固定配置)
volatile const __attribute__((__section__(".YOPEN_PARTITION_TABLE"))) YopenPartionTable g_partiontable =
{
.magic = 0x98765432,
.ap_base = AP_FLASH_LOAD_ADDR,
.ap_size = AP_FLASH_LOAD_SIZE,
.fs_base = FLASH_FS_REGION_START,
.fs_size = FLASH_FS_REGION_SIZE,
.fota_base = FLASH_FOTA_REGION_START,
.fota_size = FLASH_FOTA_REGION_LEN
#ifdef BUILD_YOPEN__SECUREBOOT_224_ENABLE
,
.secBootTable = {
.magicnumber = 0x12345678,
.blPubKey = {0xa8,0xfa,0xe6,0xfe,0x68,0x78,0x3c,0x70,0x4,0x7a,0x97,0xc8,0xbb,0x6a,0x22,0xeb,0xc1,0xa7,0x61,0x99,0xd6,0x4d,0xf3,0x6e,0xb1,0xdf,0xdf,0x6,0xe3,0x3d,0xdc,0x40,0x83,0x4a,0x7c,0x6b,0x4e,0xdd,0xdd,0x64,0xf0,0x42,0x71,0xba,0x7f,0xe2,0x3a,0x67,0x62,0x19,0xab,0xb6,0x1d,0x30,0x33,0xc8},
.verifyPubKey = {0x7d,0x46,0x37,0x35,0xe5,0x98,0x93,0x65,0xac,0xa0,0xa1,0xaf,0x6b,0x2e,0x55,0xfc,0xa8,0xf8,0x67,0xf0,0x29,0x46,0x95,0xab,0x31,0xee,0x5,0x3f,0x8,0x1,0xef,0x16,0xe5,0x17,0xda,0x77,0x84,0x4c,0x5c,0xb7,0xc0,0xcb,0xb,0xff,0x22,0x69,0x56,0x44,0x55,0x25,0x2d,0x3c,0x7f,0xb6,0xd1,0x40}
}
#endif
};
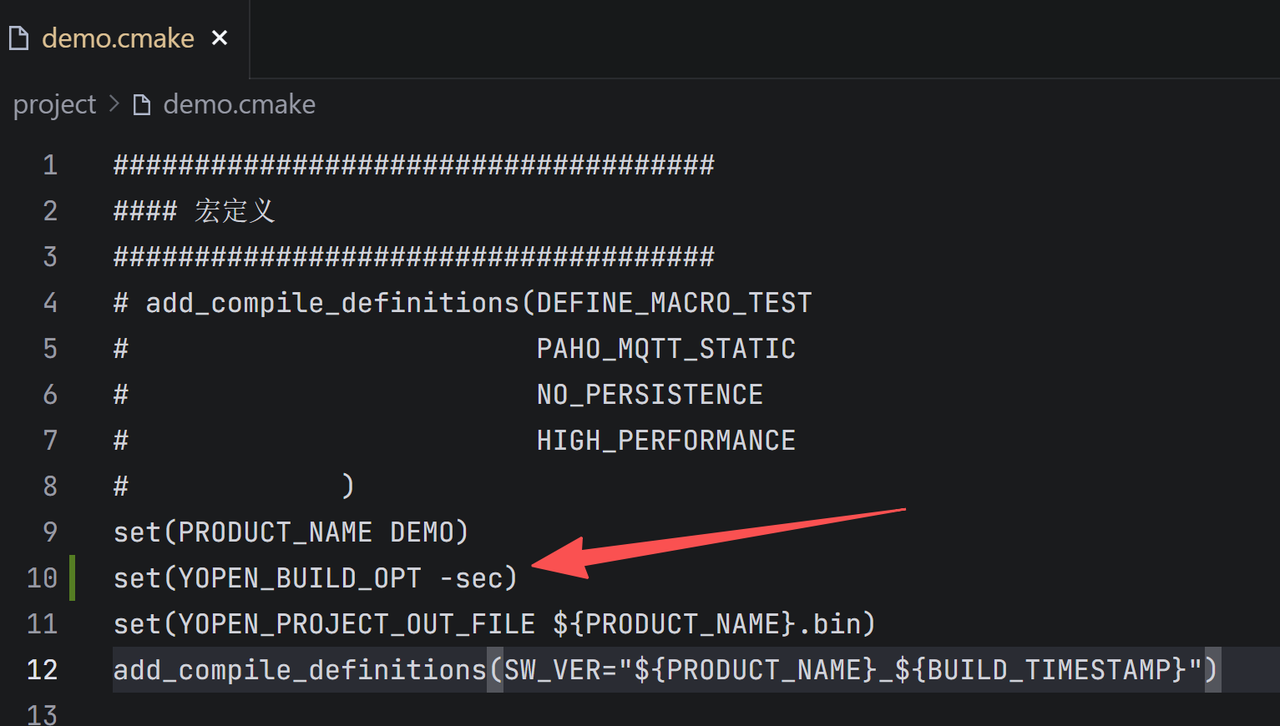
- 修改编译参数, 以demo为例
修改project\demo.cmake文件, set(YOPEN_BUILD_OPT -sec), 编译时会自动生成加密文件,并打包到binpkg中
软件编译¶
- clean
.\build.bat YM310_W09S.H60 demo clean
- 编译
.\build.bat YM310_W09S.H60 demo
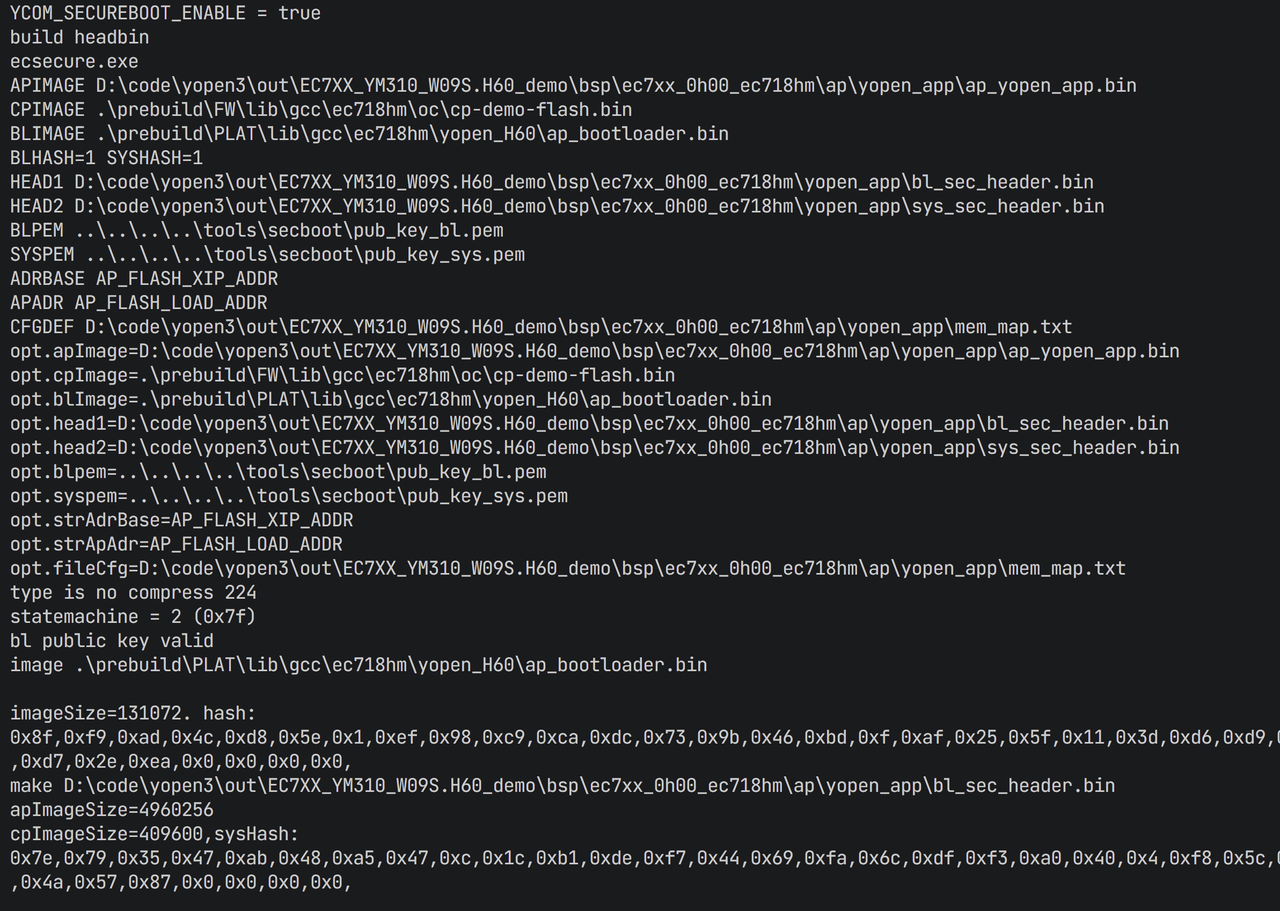
编译成功的相关日志
固件下载¶
- 选择\out\EC7XX_YM310_W09S.H60_demo下面的DEMO_USB.ini配置文件
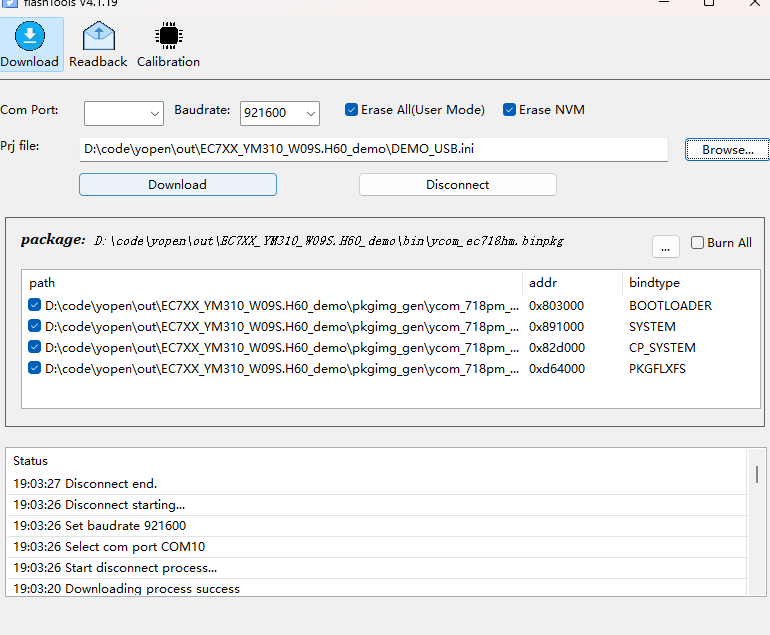
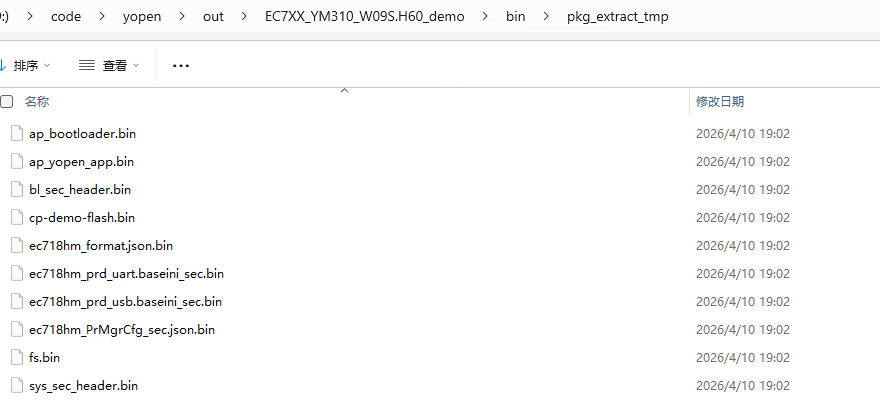
- 选择ini后会自动解压bin,如下图
EC7XX_YM310_W09S.H60_demo\bin\pkg_extract_tmp
里面包含加密文件bl_sec_header.bin和sys_sec_header.bin
- 直接选择AT口下载, 或者直接进入boot方式下载
下载工具和详细流程: http://716.yuge-info.com/tool/%E4%B8%8B%E8%BD%BD%E5%B7%A5%E5%85%B7%28FlashTools%29%E4%BD%BF%E7%94%A8%E6%8C%87%E5%8D%97/
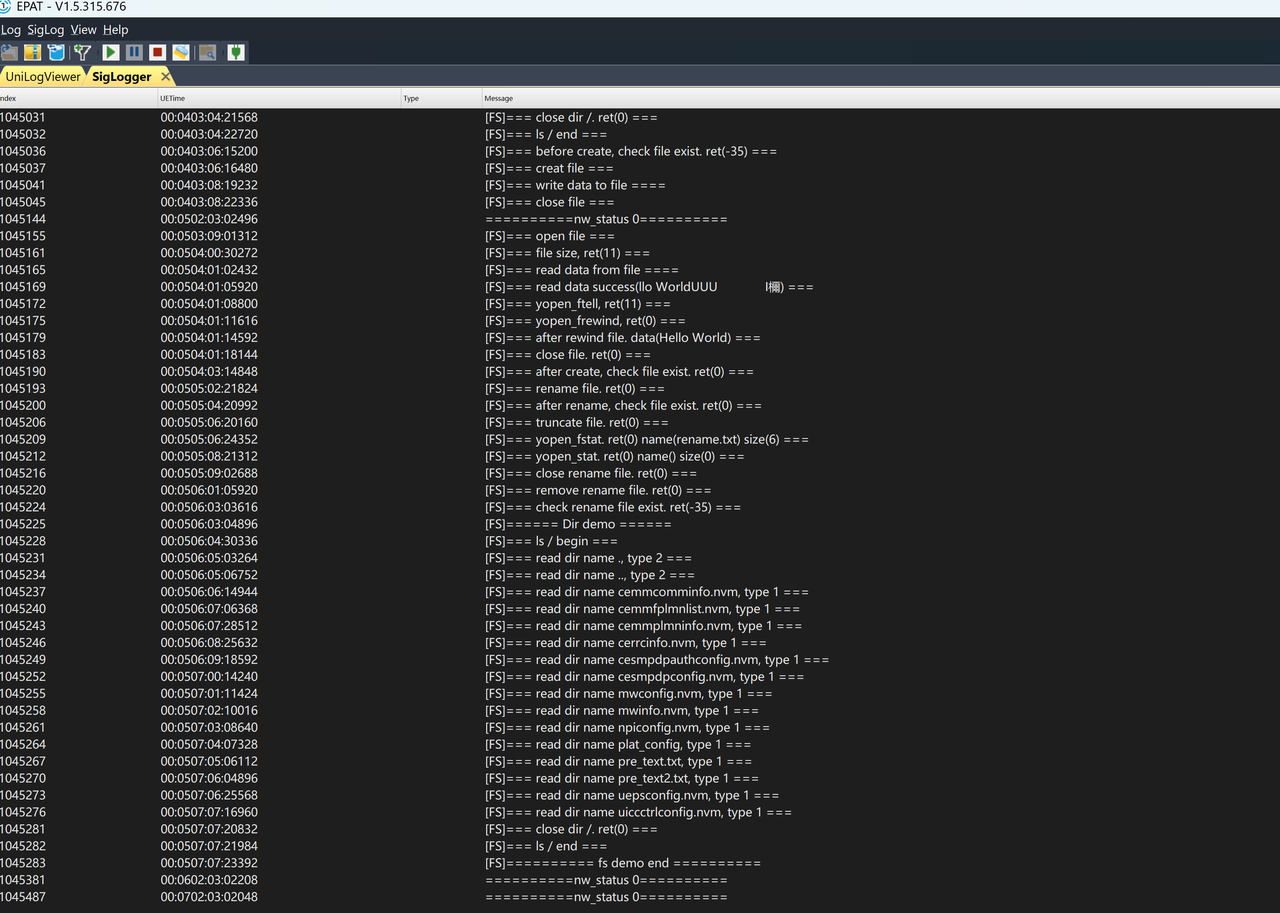
开机日志¶
debug口(UART0)¶
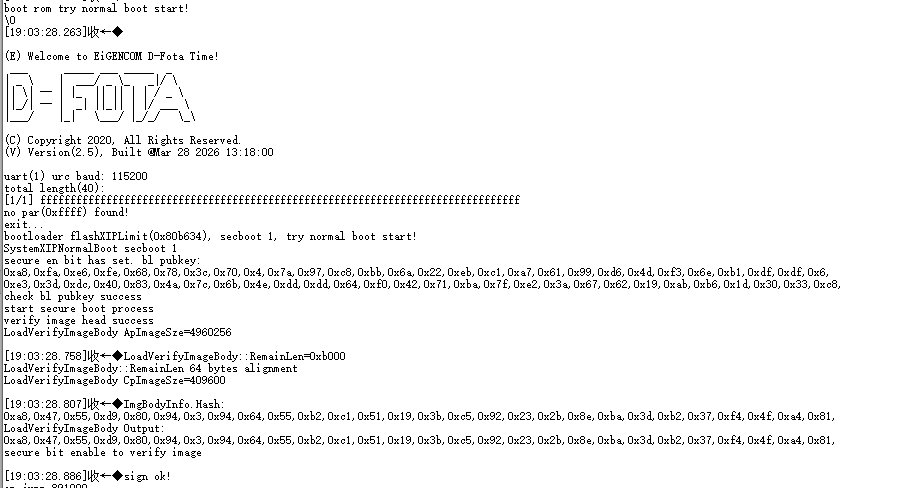
USB口¶